Images of anonymity

Introduction
The term ‘anonymity’ characterises a particular type of social relationship in which identifying information about a person is unavailable, perhaps actively withheld. Anonymity manifests in social interactions and transactions, or in the ways in which certain types of information are detached from these interactions. Images that deal with anonymity therefore often refer to the visual sources of identification (like the face, fingerprints, DNA visualisations), to communication techniques through which such information is conveyed, and to the transformation of these sources by means of masks or codes. Such images generally remain metaphorical of anonymity which can only be indicated, while this relation itself it is a cognitive state that is not visually given.
This essay deals with some of the contemporary visual representations in which anonymity comes into play. It includes examples of press images as well as images taken in artistic and scientific contexts, which it loosely collates into four sections, relating to anonymity in public space, involuntary and voluntary masks, forensic techniques of identification, and the desire to overcome enforced anonymity. The selection presented here is not intended as a definitive classification, but as an attempt at circumscribing the visual field of anonymity. Neither are all the possible variants of contemporary anonymity arrangements covered by the following examples – aspects like the anonymity of money, anonymous sperm and egg donations, or anonymous online browsing environments like 4chan or the Tor network are not addressed here, nor are related artistic practices (like for instance the complex Status project flow-charts with which British artist Heath Bunting maps the administrative construction of legal personas, or the bitcoin-based shopping spree by Mediengruppe Bitnik’s Random online shopper), many of which are conceptual rather than visual in nature.
The human face plays a particularly prominent role in images of anonymity. Homing in on what Dutch critic Daniël de Zeeuw has referred to as ‘mask culture’, the opening image of this essay points to the multiplicity of meanings associated with anonymity: this mask, originally a stylised portrait of the English Catholic revolutionary Guy Fawkes and adopted a.o. by the Anonymous hacker collective, appears here in a transparent version crafted by the artist Aram Bartholl. Like the questionable protection offered by this mask, anonymity is never absolute, but relative to the context and the particular circumstances under which it is constructed and performed. In many cases, it is merely imagined, though no less empowering and affective.
Aram Bartholl: How to Vacuum Form, multiple, 2012. Photo courtesy of the artist.

Catalogued. Crowded urban spaces are the epitome of anonymous social environments. Many people moving around, doing their own thing, not knowing each other – and in many cases not wanting to know each other. Social theorists of modernity have described the city as a site of both alienation and of freedom from obligations that come with communitarian and intimate sociality. The short video Catalogue by Chris Oakley (produced in 2004, several years before people started carrying smartphones as their personal tracking and data transparency devices) develops the vision of a shopping mall in which the visitors are identified by a surveillance system that correlates their customer type and previous consumption to their behaviour in the situation observed in situ as they look at shop windows, pay attention to advertising posters or not, and examine garments and other products, try them on, etc. While these people remain anonymous to each other, they appear as fully identified and made transparent as subjects of the technological system that controls and informs this site of consumption.
Chris Oakley: Catalogue, video still, 2004. Photo courtesy of the artist.

Camouflage. Social relationships, whether unequal or equal, are based on reciprocity. The figure of MacGhillie, proposed by the artist group Knowbotic Research, subverts such reciprocity. Neither the face of the wearer nor his or her body can be seen. The figure oscillates between the hyperpresence of a mask and visual redundancy. It traverses the modern urban environment in which conspicuity holds ambivalent currency, wavering between cumbersome affirmation and visual arbitrariness. MacGhillie is a vague presence, an anonymous figure without identity, a void in the social system. Donning the camouflage suit offers the chance to temporarily withdraw from the normal subject position and ‘become MacGhillie’. The participative action implies a fundamental questioning of interpersonal relationships based on mutual recognition and trust. MacGhillie is not necessarily a tragic, solipsistic figure, unable to enter social relations; instead, camouflage is a cunning instrument of self-empowerment and control over one’s social identity through its negation.
Knowbotic Research: MacGhillie, urban intervention, 2009. Photo courtesy of the artists.

Commons. Because of its current technical protocols, any data transaction on the Internet leaves digital traces in log-files, on servers and routers, many of which are subject to the control not only of the respective system operators, but also to the online surveillance by state and private, so-called security services. The documents made public by Edward Snowden testify to the comprehensiveness of global online surveillance by the US National Security Agency (NSA) and their international partners. They highlight the technical challenge for any attempt to establish in online communication and transactions the levels of anonymity which were, in the past, customarily expected in private conversations or cash acquisitions. Will there be a growing differentiation in social protocols and practices around anonymity, while on the technical level, substantial anonymity will increasingly be eroded? Will the technical implementation of anonymity require clandestine tools like the Dead Drops which are non-private USB devices available for data storage and sharing, cemented into the cracks of the built urban infrastructure?
Aram Bartholl: Dead Drops, public interventions, 2010-2012. Photo courtesy of the artist.

Inconspicuous. Over a period of two months, in the summer of 2009, Serbian artist Milica Tomic visited sites of the armed struggle of Yugoslav partisans against German occupation during the Second World War. During these walks, Tomic was carrying a gun – as casually as possible, she says, as though she was carrying a plastic bag. The photos and videos taken during these repeated walks document the marking and mapping of the sites where the clandestine acts of resistance took place. An unintended outcome of these performances was the realisation that people in the city streets barely took any notice of this anonymous woman-in-the-crowd carrying a gun, and nobody ever called the police, or tried to stop her. One could speculate that the militarisation of the Serbian society was, just over ten years after the wars in Croatia, Bosnia, Kosovo, still so intense that seeing a weapon in public seemed normal. Or that the level of social disengagement was so high, that nobody really cared.
Milica Tomic: One day, instead of one night, a burst of machine-gun fire will flash, if light cannot come otherwise, photo / video action, 2009. Photo courtesy of the artist.

Bagged. This photo of a detainee whose identity is being concealed by means of a black bag won the World Press Photo Award in 2004. It is reminiscent of the infamous images of acts of abuse against prisoners in Abu Ghraib and of those from the US camp in Guantánamo Bay where prisoners have been regularly kept in obtrusive orange overalls and with similar black bags over their heads. The concealment of the face is an act of power that articulates the conditions and regimes of identity and anonymity. The dehumanising gesture of hiding the head in a bag – a bag that might just as well function as a container for the head after it has been severed from the body – is here contrasted and amplified by the caring gesture towards the child whom the detainee is holding in his arm, protecting it as well as possible from the sun. The child is perfectly calm, exhausted perhaps, fully accepting the protection as though coming from a parent. What the photograph does not show, and what the bag also conceals, is whether the lips of the detainee are moving, and whether he might be whispering to the child words of love and comfort or words of hate and insurrection.
Jean-Marc Bouju: Iraqi War Prisoner, photograph, 2003. Photo copyright AP / Picture Alliance.

Codes. One technique of anonymisation implies the replacement of names by impersonal numbers and other codes and the inscription of bodies with these codes – in this case with a waterproof pen, in others by means of tattooing, like in the Nazi concentration camps where identification numbers were tattooed on the inmates’ forearms. In a database, such more or less unchangeable physical features like birthmarks, tattoos, or missing or deformed limbs, would be documented and permanently connect the number to a name, the durability of the mark inscribing identifiability on the body. But why are the eyes of the arrested man bandaged? What is it that he is not supposed to see? The face of the soldier who so readily allows the photographer to shoot a picture, over his shoulder? Or the face of the photographer? In this scene, whose identity is being concealed from whom? Which information is withheld, and which information is added? Who can read the codes of identification?
Jacob Silberberg: Haditha, Iraq, photograph, 2005. Photo copyright AP / Picture Alliance.

Blur. In a digital portrait image, pixelation signifies that the facial features and identity of the person are known, and that this knowledge is deliberately withheld from the public eye. It is a visual code applied in the mass media, a media effect. The computer on which these image files are stored and through which the pixelation has been applied, holds the undistorted portraits. They are not shown themselves, but their digital masking testifies to the authenticity of the portraits and the existence of the accused.
Photo clipping, Rheinische Post, 27 September 2007.

Dangerous reward. The protection offered by a mask can have many reasons. Here an informant to the police in the Philippines is publically rewarded for having provided crucial information that led to the capture of an Islamist terrorist leader. Any particular physical markers are hidden behind a black mask, white gloves, generic clothes. Most striking in the photograph is perhaps the smile of the plain clothes officer who hands over the suitcase with the money and who appears certain that he knows the person hiding under the mask – an anonymisation that is meant only for some of those present, while others feel a gratitude towards the person whose identity they help obfuscate. The danger from which the mask protects the informant comes from two sides: from the accomplices of the captured terrorist who might seek revenge from a traitor, and from those observers who are envious and would like to obtain a part of the reward money. The moment of removing the mask, the moment of revelation and transformation, is always highly precarious.
Laurenz Castillo: US embassy officials and informants, Philippines, photograph, 2007. Photo copyright dpa - Report / Picture Alliance.

Prize. In this image the relationship of masked and openly visible faces is reversed: the guys with the guns hide their faces behind what looks like traditional cloth, while the kidnappee is clearly identifiable. Showing his face is the main purpose of the image, the promise of the prize that is his safe return if the ransom is paid, or other conditions set by the kidnappers are met. The second most important aspect are the guns, which testify to the possibility to kill the captive and, as marked by the bazooka leaning in the background, launch attacks against larger targets. This is a gamble in which the faces of the kidnappers are unimportant. What Roland Barthes called the punctum, the point of attraction that appears to form the emotional hinge of the photograph, are the eyes of the squatting kidnapper who observes the victim with puzzling care.
Stringer, Hostage, Afghanistan, photograph, 2007. Photo copyright Reuters.

Equals. In the summer of 2007, German special police forces arrested members of a supposed Islamist terrorist group which, in correspondence to the region where they were based, became known as the Sauerland Gruppe. All four men in the photograph are wearing balaclavas which make them appear very similar – unidentified members of the tribe that does not want to be recognised in press photographs like this one. The detainee is hand-cuffed and wears a blue overall which the police may have brought to the early-morning arrest. His anonymisation protects his civil rights that prevent public exposure. A carefully choreographed scene, down to the handsome automatic weapon camouflaged in front of the grey jacket.
Ronald Wittek: German Federal Police officers and suspect, photograph, 2007. Photo copyright DPA / Picture Alliance.

Green veil. The woman’s face is covered by green cloth, darkened glasses shield her eyes from the sun and from unwanted gazes. The hair which a veil is normally supposed to hide, proudly towers her forehead. There is a man standing beside her, his face clearly recognisable, his mouth pasted shut with an x-shaped green tape. The gesture he makes with his right hand – a Victory-sign composed of forefinger and middle finger, both tightly wrapped in shiny green tape – seems to embrace the woman, even though, on second sight, we understand that she is standing in front of him, and only the medial effect of spatial compression due to the optics of the tele-lense pushes their images together, closer than the two people actually are. As it appears in this press image, the woman’s form of public protest is one of passive resistance, of hiding her face and turning the religious demand of covering her head into an act of anonymisation and defiance. Under which circumstances will she reveal her face?
Photo Ghalam News, Iran, 2009.

Being Leo Selvaggio. How to avoid being identified by public surveillance cameras and facial recognition systems, including those in people’s smartphones? If you wear a balaclava, or show up as MacGhillie, you’re likely to draw unnecessary attention. The American artist Leo Selvaggio is offering his own face as a basis for masks that people can buy or produce themselves, and wear in public. Similar to the multiple copies of the same Payback customer card issued by the Foebud media activist association a few years ago, Selvaggio’s URME Mask multiplies and diffuses his own facial identity and, at the same time, offers it as an anonymising shield for others. While they walk around as though they were Leo Selvaggio, he himself is henceforth only one possible wearer of the face and his identification would require immediate physical examination, rather than visual surveillance at a distance.
Leonardo Selvaggio: URME Personal Surveillance Identity Prosthetic, 3D-printed mask, 2014. Photo courtesy of the artist.

Portrait parlé. The concept of a personal identity which is disrupted by anonymity, is itself an invention of the modern era of Western civilisation. According to Michel Foucault, the emergent forms of governmentality of the 18th century required – first in Europe, then also in its colonies – an unambiguous relation between bodies, names, and social personas. The inscription into administrative, labour and juridical relationships created the modern subjectivities of individuals who would – reluctantly or proudly – say ‘I’. The French police administrator Alphonse Bertillon, one of the engineers of such modern identity regimes, conceived the portrait parlé to enable ‘signaletic identification’: measurements taken of different body parts, combined with a standard frontal and profile portrait photograph. The latter was, notably, not regarded as the primary source for identification, but only as subsidiary, since the usefulness of such a picture depended on intuitive recognition, rather than on the objective reliability of skull circumference, ear shape, or finger prints (which are missing on this fiche which Bertillon made of himself).
Alphonse Bertillon: Portrait parlé, Alphonse Bertillon, identification card, 1912.

Inversion. The trial against OJ Simpson in a US court made extensive use of DNA traces that were found at different sites and presented as proof of the identity of the supposed murderer. The court case was embedded in a media environment in which the forensic methods employed by the police were popularised by the ‘CSI’ TV series that inflated trust in the reliability of such methods. At the same time, the case became the site of their intense public critique. Against the popular belief that the visualisation of a DNA sequence is a fixed and recognisable ‘portrait’ of a specific person, the Bio-Art activist Paul Vanouse staged a performance in which his collaborators instructed the audience in creating such visualisations. The aim was to inform them about the degree to which the visual outcome of the procedure varies and is predicated on specific technical methods, materials and choices taken. The Simpson trial, as Vanouse affirms, was then also the first such case in which the defence team was technically informed enough to successfully challenge the supposed DNA-related evidence put before the jury.
Paul Vanouse: Suspect Inversion Center, SIC, Clipboard from installation at Schering Foundation, Berlin, 2011. Photograph by Axel Heise. Photo courtesy of the artist.

Constructions. In a series of artificial human faces, the artist Heather Dewey-Hagborg speculates about the presumed possibility of gleaning physiognomic information from DNA traces found, for instance, in the street in the form of human hair, or saliva on cigarette butts. The presence or absence of certain genes in these DNA samples suggest the likelihood of specifications regarding race, gender, eye-colour, nose size and shape, or obesity. In order to arrive at a fully shaped face – rather than at a loose assemblage of abstract features – the results have to be extrapolated to an extent that what are really random or highly generic choices appear, in plastic representations like these, as unique features. The recognisability is disconcerting, especially because there is no way to confirm or disclaim any real similarity that may exist between the person who threw away the cigarette butt, and these artificial, phantom features. Since the procedure is in use and requires critical public engagement, Dewey-Hagborg has decided to make the code publically available that she continues to develop for her project.
Heather Dewey-Hagborg: Stranger Visions (East Hampton 7), 3D-printed portrait, 2012. Photo courtesy of the artist.

Archaeology. The murder of political opponents and prisoners and their anonymous burial in individual or mass graves is one of the methods of annihilation that have been used in recent decades by dictatorial regimes all over the world – in Argentina, in El Salvador, in Iraq, in Iran. The practice of ‘counter-forensics’ as described by the artist and critic Allan Sekula, is employed to recover the identity of those carelessly buried bodies. The archaeological work to be done includes many steps and requires the observation and documentation of the henchmen and the grave-diggers, the identification of burial sites, the digging and careful removal of covering earth and materials, the recovery of significant bodily remains and their coupling with identifying markers, culled from the memories of surviving family members and acquaintances. These efforts involved in reconnecting information, reversing the cuts of anonymisation, give an indication of the work that is involved in any countering of anonymity, in the marking and creating of identities, sources, origins.
Susan Meiselas: An international forensic team organized by Middle East Watch and Physicians for Human Rights work at a mass grave site in Koreme, Northern Iraq (Kurdistan), photograph, June 1992. Photo copyright Susan Meiselas / Magnum Photos.

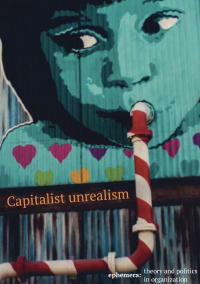
Operational images. The form of display in this widely publicised aerial image suggests that the portrait it shows has a target audience of only one: the drone pilot who, perhaps, considers launching a deadly attack on the house next to the field where the oversized picture of a child has been placed; the implicit claim being that the depicted child lives in the house and would be killed if the house was bombed. However, for over a hundred years the history of aerial military reconnaissance has been a history of camouflage and counter-camouflage, hiding military installations under seemingly natural covers on one side, and employing specially trained people who recognise the camouflage and identify the relevant target hidden beneath it on the other. The anonymity of the dangerous or innocent homestead is given a face which it can only wear like a mask, since there is no way that the truth about the inhabitants can be directly communicated to the remote viewer on a computer console in Nevada, or Arizona. Like for the wearer of Selvaggio’s URME Mask, identification would require an immediate encounter.
#NotABugSplat, Khyber Pakhtunkhwa region, Pakistan, hand-out, 2014. Photo copyright AFP/Getty Images.

Insertion. While somebody has requested for the facade of Borsigstraße 4 in Berlin to be concealed from Google Streetview, which is why in this image the area to the left appears as a translucent blur, the artist Aram Bartholl decided to run after the camera car and seek its attention, and the attention of uncounted Google Streetview users who examine that part of the Earth by means of the online service. Somewhat frustratingly, his face – like any other face or number plate that Google’s visual recognition software detects in these photographic images – is also blurred and recognisable only to people who are familiar with Bartholl’s characteristic physique. On the image files stored on servers of the company itself, faces, number plates and facades are of course properly visible, waiting for examination and further usage.
Aram Bartholl: 15 seconds of fame, performance, 2010. Photo courtesy of the artist.
Barthes, R. (1981) Camera lucida. New York: Hill and Wang.
Brunton, F. and H. Nissenbaum (2016) Obfuscation. A user’s guide for privacy and protest. Cambridge, MA: MIT Press.
Deseriis, M. (2015) Improper names: Collective pseudonyms from the Luddites to Anonymous. Minneapolis: University of Minnesota Press.
Federrath, H. (ed.) (2001) Designing privacy enhancing technologies. Design issues in anonymity and unobservability. Berlin: Springer.
Foucault, M. (1975) Discipline and punish: The birth of the prison. New York: Random House.
Keenan, T. (2014) ‘Counter-forensics and photography’, Grey Room, 55: 58-77.
Knowbotic Research and A. Broeckmann (eds.) (2010) Opaque presence. Manual of latent invisibilities. Berlin and Zürich: Diaphanes/Edition Jardins des Pilotes.
Levin, T.Y., U. Frohne and P. Weibel (eds.) (2002) CTRL [SPACE]: Rhetorics of surveillance from Bentham to Big Brother. Cambridge, MA: MIT Press.
Sekula, A. (2006) ‘A portable National Archive for a Stateless People: Susan Meiselas and the Kurds’, Camera Austria, 95: 9-11.
de Zeeuw, D. (2017) ‘Immunity from the image: The right to privacy as an antidote to anonymous modernity’, ephemera, 17(2) [this issue].
Dr Andreas Broeckmann is an art historian and curator who lives in Berlin. He works as the curator of the Leuphana Arts Program in Lüneburg and is currently a guest professor for Art and Media at Universität Oldenburg. He is the author of Machine art in the twentieth century (2016) and lectures internationally about the history of modern art, media theory, machine aesthetics, and digital culture. Broeckmann holds a PhD in Art History from the University of East Anglia, Norwich/UK. He has curated exhibitions at major European venues, incl. transmediale, Stedelijk Museum Amsterdam, Van Abbemuseum Eindhoven, and Hartware MedienKunstVerein Dortmund.
Email: broeckmann AT leuphana.de